Caronte
From Raw Payload to Actionable Intelligence in Minutes.
Stop waiting days for manual malware analysis. Caronte orchestrates autonomous alert triage, safe malware detonation, and LLM-powered reverse engineering. We translate complex, obfuscated threats into clear, actionable Indicators of Compromise (IoCs) at machine speed, empowering your SOC with the exact intelligence needed to block attacks instantly.
Book a Demo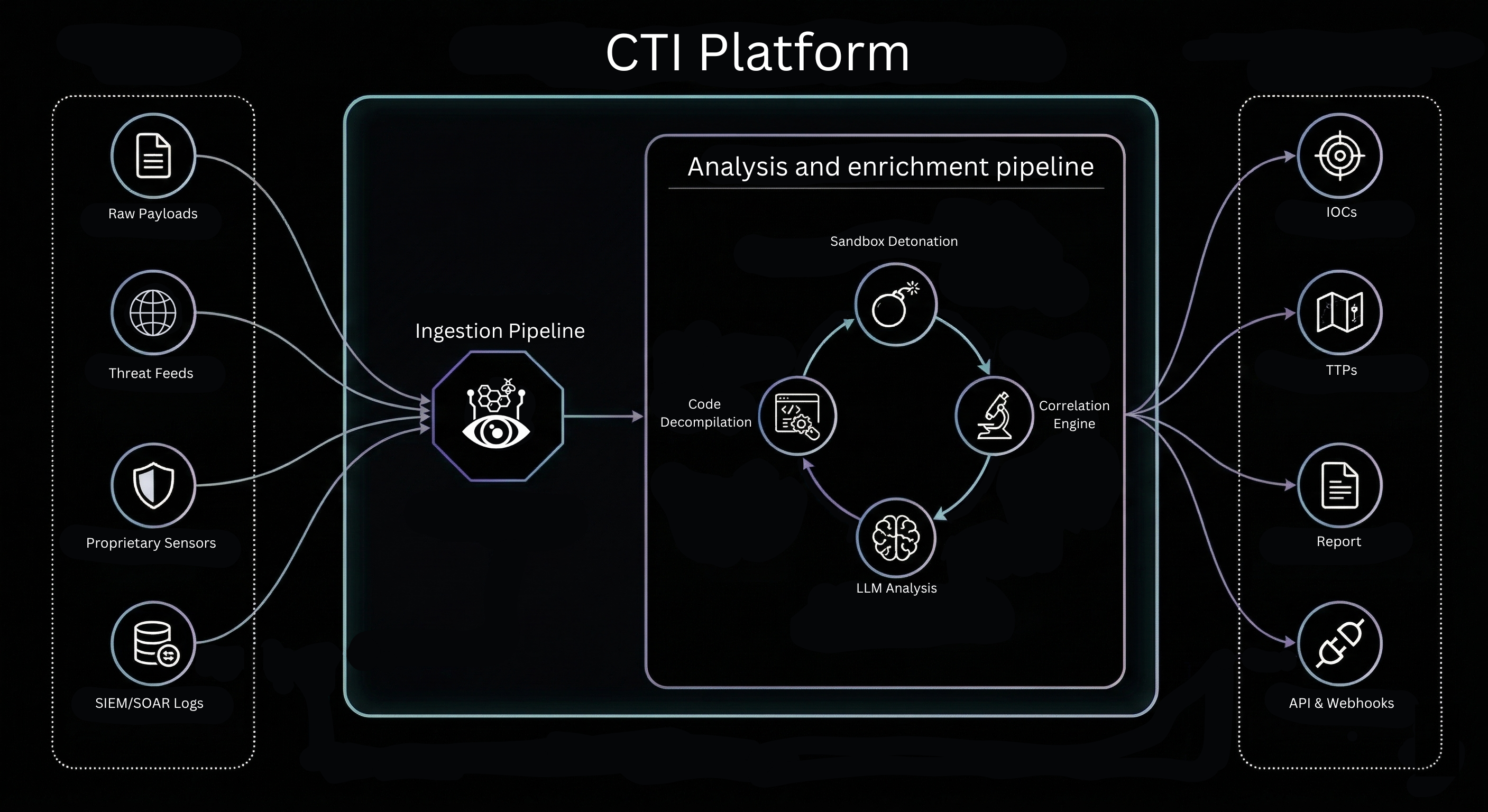
Autonomous Reverse Engineering
When unknown threats are intercepted by our sensors or manually dropped into the platform, they are funneled into our specialized intelligence hub. We leverage powerful native LLMs fully integrated with military-grade reverse engineering tools to decompile, inspect, and analyze malicious code with complete autonomy. The system de-obfuscates strings, identifies system calls, and explains the malware's true intent in plain English.
Core Features
Autonomous Alert Triage
Stop drowning in alert fatigue. Our autonomous engine ingests, normalizes, and correlates global threat feeds with internal telemetry. Acting as a tireless threat hunter, it filters noise to instantly expose hidden adversary infrastructure, active campaigns, and complex attack patterns.
Automated Code Decompilation
Transform days of specialized manual analysis into minutes. Our system autonomously reads decompiled output, translating complex assembly code and zero-day payloads into plain English reports. We extract precise TTPs and actionable IoCs instantly, empowering your SOC to block threats.
Safe Detonation Sandbox
Execute suspicious payloads within a heavily instrumented, isolated environment. We safely detonate zero-day malware to capture precise behavioral data, memory dumps, and network callbacks. This generates instant, audit-ready forensic reports, empowering your SOC team to orchestrate machine-speed containment.
Threat Actor Infrastructure Mapping
Move beyond analyzing isolated samples. Our autonomous engine correlates IoCs across global threat feeds to map the adversary’s complete infrastructure. By identifying shared hosting, reused certificates, and command-and-control patterns, we expose the attacking group's entire operational footprint in real time.
Frequently Asked Questions
The sandbox supports all common malware formats including PE executables (.exe, .dll), scripts (PowerShell, Python, JavaScript, VBScript), documents (PDF, Office macro-enabled files), and archives (.zip, .rar).