Arcangelo
Continuous Adversarial Simulation, 24/7.
Move beyond static, annual penetration tests. Arcangelo delivers continuous, autonomous adversarial simulation across your entire attack surface. By safely executing sophisticated attack campaigns against your hybrid IT infrastructure and internal AI models, we expose critical blind spots and validate your defenses before real attackers strike.
Book a Demo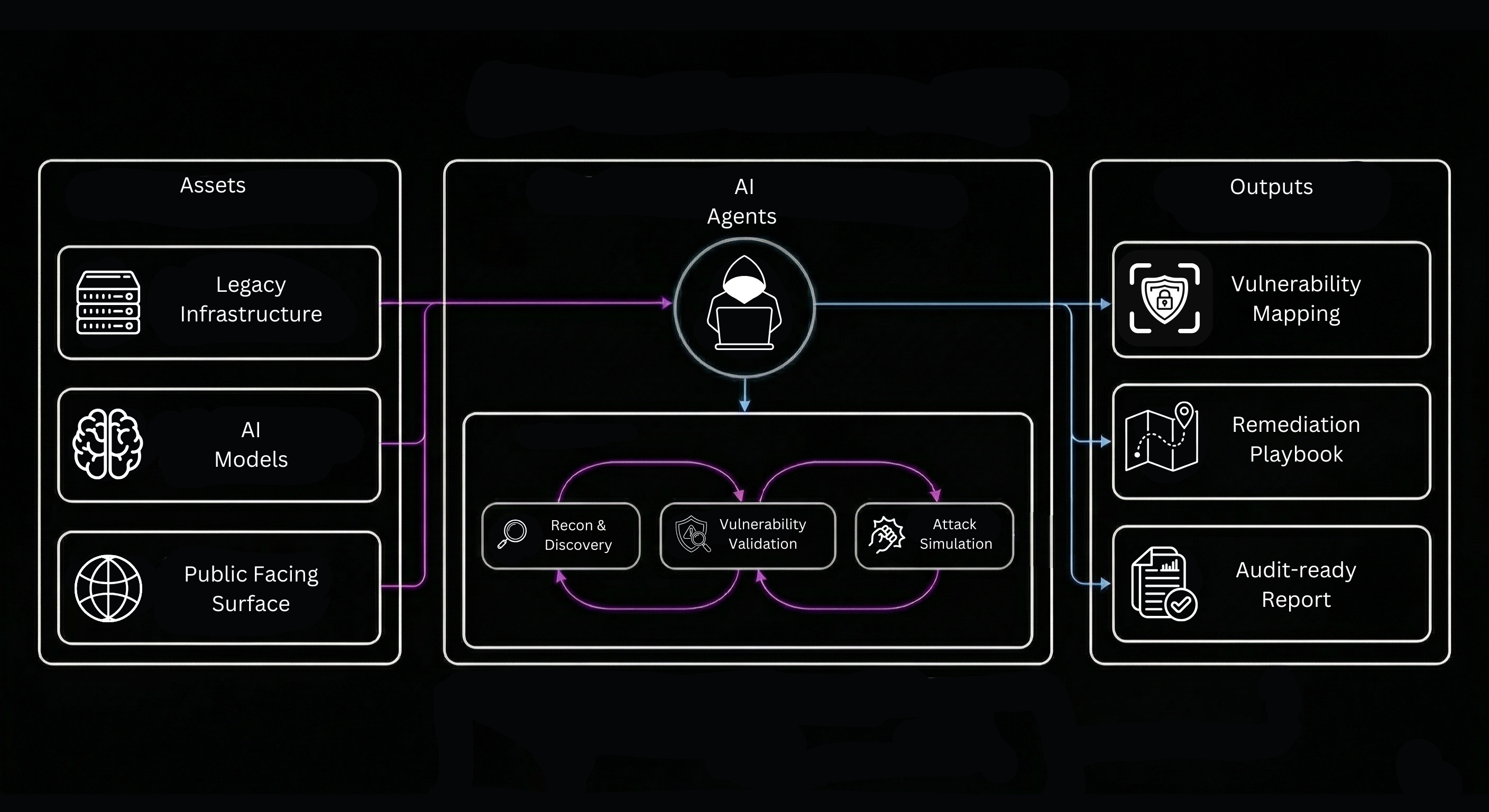
Continuous Adversarial Simulation
Security posture degrades the moment a penetration test report is delivered. We solve this by deploying autonomous AI agents that act as a persistent, highly skilled Red Team. Operating safely within your environment, these agents continuously execute the latest threat behaviors, from complex lateral movement to advanced prompt injections. This provides real-time, measurable proof of your resilience and ensures constant compliance readiness.
Core Features
AI Model Stress Testing
Validate your enterprise LLMs and autonomous agents for safe deployment. We continuously execute sophisticated jailbreaks, semantic attacks, and prompt injections against your models, generating the irrefutable, audit-ready proof of resilience required by modern AI compliance frameworks.
Continuous External Reconnaissance (EASM)
Map and monitor your entire public-facing attack surface. Our autonomous engine continuously scans the open and Dark Web for exposed assets, leaked credentials, and shadow IT, revealing exactly what adversaries can exploit before they ever touch your perimeter.
Legacy Infrastructure Validation
Test the limits of your legacy network perimeter and internal segmentation. Our autonomous adversaries simulate real-world APT campaigns, executing credential harvesting and lateral movement to expose the exact breach paths hidden within your Active Directory and cloud environments.
Actionable Remediation Paths
Move beyond endless lists of theoretical vulnerabilities. Every successful simulation generates a prioritized, step-by-step remediation plan mapped directly to the MITRE ATT&CK framework. We empower your engineering teams to proactively close the exact security gaps real adversaries would exploit.
Frequently Asked Questions
A traditional pentest is a point-in-time snapshot, valid only on the day it was run. Every new deployment, configuration change, or employee added to Active Directory introduces new risk. Our platform runs continuously, meaning you always have an up-to-date picture of your true security posture, not a stale report from six months ago.