The AI-Native Security Platform
Adaptive AI Deception
Full-Stack Visibility Across Your Entire Infrastructure
Deploy high-interaction runtime deception sensors everywhere attackers move: Kubernetes, multi-cloud, APIs, IoT, and enterprise AI agents. Our fully managed platform deploys serverless traps in minutes with zero operational overhead. When zero-day exploits and supply chain attacks bypass your perimeter, adaptive deception is the only way to expose hidden lateral movement.
Autonomous SOC & Intelligence
Instant Containment & Cyber Threat Intelligence (CTI)
Transform silent compromises into actionable intelligence in minutes. Our CTI hub safely detonates zero-day malware in isolated sandboxes to extract precise IoCs and TTPs. Simultaneously, our autonomous AI SOC leverages these insights to instantly contain threats and generate executive-ready forensic reports. Slash MTTR to seconds and cut SOC costs by 60%.
Continuous Threat Validation
Continuous Validation with Arcangelo
Stop waiting for adversaries to strike first. Our platform acts as a persistent, automated red team, continuously mapping your attack surface and executing safe, real-world campaigns against your network and AI models. Expose critical vulnerabilities and validate your defensive posture before attackers exploit them. Ensure your SOC is always ready to defeat the latest AI-enabled threats.
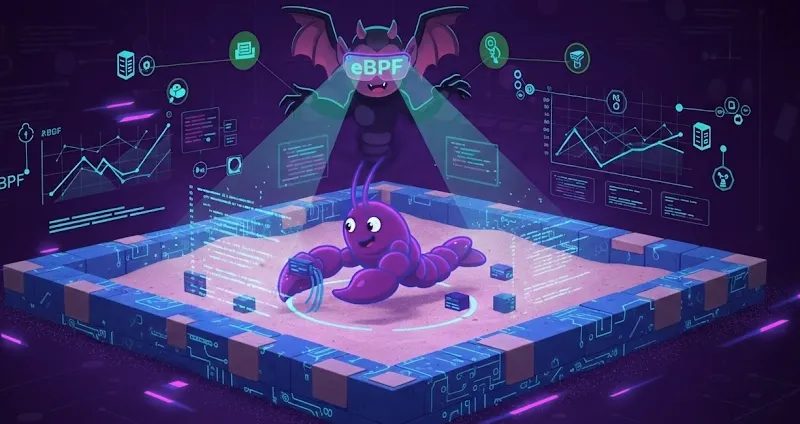
How Beelzebub Works
1) Deploy Runtime Deception Sensors
Deploy high-interaction runtime deception sensors across your entire infrastructure: Kubernetes, multi-cloud, APIs, IoT, and enterprise AI agents. Our fully managed cloud platform creates realistic, vulnerable-looking assets in minutes without disrupting production workloads. Zero operational overhead, zero false positives, only confirmed threats trigger alerts.
2) Engage & Extract Intelligence
When attackers interact with our sensors during lateral movement, our adaptive AI keeps them engaged in a completely isolated environment. Simultaneously, our CTI hub performs comprehensive threat analysis, safely detonating zero-day malware in sandboxes and inspecting payloads to extract precise TTPs. Turn attacker persistence into your actionable intelligence advantage.
3) Autonomous Response
Leveraging the extracted intelligence, our autonomous AI SOC isolates compromised assets in seconds, permanently stopping lateral movement. The platform instantly generates executive-ready forensic reports with clear remediation steps, eliminating manual triage. Transform hours of manual incident response into seconds of autonomous, precision containment.
Enterprise Compliance & Regulatory Alignment
Ensure strict compliance with the lateral movement detection and incident reporting requirements mandated by NIS2, DORA, EU AI Act, and SOC 2. Beelzebub provides total post-breach visibility and undeniable audit trails for every intrusion attempt. Trusted by Fortune 500 leaders across telecommunications, finance, and critical infrastructure.
Security Lab
Actionable intelligence, deep-dive malware analysis, and zero-day research directly from the Beelzebub threat hunting team.
Runtime Tracing for AI Agents: What Your OpenClaw Agent Actually Does Inside the Container
Read MoreWatching CVE-2026-24423 Hit the Wire: A SmarterMail Honeypot Field Report
Read More
Built by security practitioners,
for security practitioners.
Every member of our core team has operated on the front lines of cybersecurity. We built Beelzebub because we lived the problem firsthand.

Mario Candela
CEO & Founder
Computer Science graduate, Cybersecurity expert with 15+ years across startups and enterprises (Daimler, Sky, Zurich, hackerone, hlpy, NTTData). Ethical hacker since childhood, creator of Beelzebub OSS, member of The Honeynet Project.

Giorgio Bordoli
Sales Engineer
Summa Cum Laude Computer Science graduate (Cybersecurity) from Arizona State University. IEEE–HKN member. Focused on translating complex security challenges into scalable, real-world solutions that protect organizations while enabling innovation.

Giovanni Braccini
R&D Engineer
MSc in Computer Science from University of Pisa, with both theses focused on deception technologies. Holder of two patents for innovative threat actor identification and threat intelligence distribution. Discovered NordVPN 2FA bypass (CVE-2025-61187).
Francesco Sardone
Head of Technology
Seasoned software engineer with a decade of experience in startups and scale-ups, building AI-driven platforms, distributed systems, and developer tools. Scaled products from early revenue to tens of millions ARR, handling millions of service requests. Passionate about programming since age 10, experienced in leading teams and mentoring, and actively contributing to open source.

Salvatore Scorsone
Head of Product
Computer Engineering graduate from Politecnico di Torino. Cybersecurity professional with hands-on expertise in Cyber Threat Intelligence, Digital Forensics, and Incident Response. Proven track record in product development and go-to-market execution for security tooling.

John Joseph Galea
CFO
Senior finance executive with deep expertise in scaling fast-growing technology companies. Strategic leader focused on capital allocation, operational efficiency, and driving sustainable financial performance in the cybersecurity sector.
Here's What People Are Saying
Cybercriminals are evolving, and so are the defenders. Beelzebub’s AI-native deception platform is flipping the script with LLM honeypots that lure and expose cryptojacking malware. 🧠 While attackers think they’re winning, Beelzebub’s AI-driven SOC is watching, analyzing, and responding in real time.
Chief Security Advisor, Microsoft
Securing Kubernetes Using Honeypots to Detect and Prevent Lateral Movement Attacks
Compliance Auditor
The initial hype about AI may cool down, but the use of AI is only really gaining in importance, especially in the case of honeypots!
Senior Expert Security, Telekom Security
Beelzebub is an open-source honeypot framework engineered to create a secure environment for detecting and analyzing cyber threats.
Cybersecurity news and industry insight
Beelzebub: Open-source honeypot framework
CISO
Beelzebub: Open-source Honeypot! AI-powered honeypot framework creates a secure, high-interaction environment to detect and analyze cyber threats. It’s designed for low-code deployment and supports multi-protocol decoys like SSH, HTTP, TCP, and MCP to detect prompt injection attacks against LLM agents. Unlike traditional honeypots, Beelzebub uses an LLM sandbox to interact with attackers safely.
Executive Director - EC-Council
The framework generates high-fidelity threat intelligence, detecting command patterns and techniques used by real attackers. The combination of realism and automation allows security teams to operate realistic honeypots without the traditional maintenance and supervision costs. Beelzebub represents a significant evolution in proactive detection: it acts as an early warning system, reduces false positives, and helps refine defenses through real operational information on attacks targeting environments with artificial intelligence.
Senior Manager, Cybersecurity at KPMG
The Beelzebub framework is an advanced honeypot that provides a very secure environment for detecting and analyzing attacks. The framework is very easy to set up and uses artificial intelligence to simulate the behavior of a honeypot.
Security Audit Team Leader - Tejarat Bank
Prompt injection is still an open threat. Beelzebub’s new MCP honeypot catches it in action,right inside your agent pipeline. Trigger logs. Attack metrics. Safer models.
Integrate seamlessly